Why your business…and your people…need to start protecting passwords with their life…literally!
Sound a bit dramatic? We meant it to! Why? Because every day, more and more, password compromises and breaches are, at best, blocking productivity and people’s ability to get their jobs done, and at worst, threatening the very existence of businesses, their financial viability, and by extension the job security of their employees.
What your password is supposed to do!
Every business has a wealth of sensitive data, financial information, intellectual property and personally identifiable information that sits in the systems their passwords are supposed to protect. Yet, statistics are telling us that over 80% of hacking-related breaches in 2017 were the result of weak, default, or stolen passwords!
What happens if your password is compromised or stolen?
This is a big deal for lots of reasons. With your password in hand, malicious actors can:
- Access and download proprietary and sensitive information housed in your email, files or systems you have access to.
- Launch phishing and ransomware attacks from your account.
- Make changes to admin controls, account settings and email forwarding rules to funnel information out of your systems.
- Monitor communication between you and others you communicate with both inside and outside your organisation with a view to launching future business email compromise or impersonation attacks.
- Sell your credentials (and those of others housed in your systems) on the dark web for financial gain.
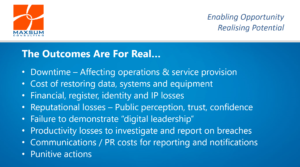
And for your business, the potential fall-out from a password-compromise data breach is massive.
The problem with passwords…
…is that while people know that they are meant to keep passwords secure, in practice, it doesn’t always happen that way!
A recent global report by LastPass into password security covering some 43,000 organisations around the world tells us that password sharing is rife in the workplace, with employees sharing an average of six passwords with their co-workers.
Not to mention all those passwords stuck on post-it notes around offices nationwide, or all the easily guessable passwords we see all the time, like people’s names, birthdays, pet names etc.
By the way, do you know what the TOP 2 consistently breached passwords are?
Closer to home, 59% of the data breaches reported under Australia’s new Notifiable Data Breaches Scheme over the April – June 2018 quarter resulted from malicious or criminal attack including phishing, malware, ransomware, brute force attack, compromised or stolen credentials, hacking, social engineering and impersonation, all of which are fuelled by poor password and credentials management. A further 36% of reported breaches on top of this were the result of human error, including entering credentials into phishing emails or disclosing passwords.
And at the coalface, we as an IT service provider have seen that nigh on 100% of data breaches we have remediated this year have stemmed from password credential failings…
Upping the Ante in Your Password Management: Top Tips!
The LastPass report also tells us that one in two organisations are struggling to maintain control of password security.
At a business or organisational level, revising password policies can refresh and strengthen your organisation’s security posture, especially if you have recently experienced a breach and want to implement better password security practices going forward. If you don’t have a password policy in place, it’s probably time to have a chat to us about implementing one in your organisation.
For individuals, choosing the most secure password possible is sometimes a compromise between security and ease of use, but having the most secure password possible will help protect your team and your organisation from compromises and data breaches.
At a bare minimum, our recommendations around password selection and management include:
- Choose a random password of 12 or more characters in length; in fact, the longer the better!
- Get creative using strings of random words in combination with upper and lower-case letters as well as punctuation and numbers.
- Do not reference information that could be easily discovered, such as your favourite footy team, pets name or birthday.
- Be sure not to follow a predictable pattern when choosing a password eg, JanPassword1, FebPassword2, MarchPassword3.
- Use a password manager with a super-secure master password.
- Do not use the same user ID and password for any two services
- Do not repeat or revise any previous passwords.
- Change your password frequently, ideally every 30,60 or 90 days depending on your system access and permissions and your organisations policies. The more regularly a password is changed, the less chance there is of it being involved in a breach.
- Once you’ve selected a new password, please ensure that you do not disclose or display your new password, thus compromising its security all over again.
Doubling Down on Password Security
By now you would have the idea that the humble password is pretty exposed to both malicious intent and human error in today’s threat landscape. To really double down on your password security and shore up your data breach prevention efforts, businesses need to take a more layered approach not only to password protection, but their cybersecurity posture in general.
The quickest and easiest way to add an extra layer of protection to the passwords to protect your sensitive, personal and propriety information is to look at implementing Multifactor Authentication.
Have a chat to us today about Multifactor Authenticator and read more about the benefits of implementing MFA right here.