Here are the remote working IT Security steps you may have missed in the rush to get remote-work ready, and how to fix them!
Long before COVID-19 many businesses were, in varying degrees, moving towards offering or embedding some form of remote working flexibility in their workplaces.
This was largely driven by changing workforce demands, the newfound flexibility that a new generation of cloud technologies, mobile devices and better internet connectivity offered, not to mention the new work-life balance demands of new generations of employees.
If you happened to be part of an IT team or work as a business services manager pre-COVID-19, you probably had some experience already in preparing laptops for staff to use remotely, and setting up mobile phones with access to company data for travelling team members, or for team members who work remotely.
But I think we can all agree, these are all very different scenarios to what we have seen over recent months where almost overnight Australia-wide whole businesses were literally were required to down tools, shut up shop, and regroup – remotely – from home.
Everything is unprecedented….until it happens for the first time
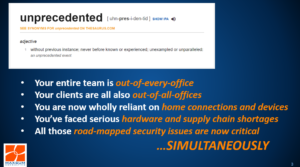
UNPRECEDENTED – This is the word of the moment getting bandied around a lot in relation to COVID-19.
Just as this is a health and economic crisis the likes of which the world has never seen before, this is also unlike any business continuity scenario the world, or indeed any business or industry en-mass, has ever seen or faced before.
Even organisations with robust business continuity plans in place most likely had not planned for a scenario where:
- Their entire team was not working from any kind of office space
- All the clients were in the same boat
- They may be wholly reliant on home internet connections and personal devices to keep the business running
- They faced serious enterprise grade hardware shortages and supply chain constraints
- They had a list of outstanding IT security issues on their roadmaps that they hadn’t gotten around to signing off on yet
- Now absolutely everyone on their team needed everything…yesterday!
- Simultaneously !!!
The No. 1 thing businesses missed in the rush to get remote work ready
So, it naturally follows that in order to fast track remote working some concessions had to be made. And with time and resources of the essence back in February/March 2020, hindsight is now showing that the biggest trade-offs made were against the fine points of remote working IT security. Most businesses’ number-one priority, and necessarily so, was just to get people and resources connected and productive.

Let’s start with the obvious – A user’s home network and cybersecurity may never be as strict, provide the same level of protection, and be as well thought out as your IT organisation in the office.
On top of this, the majority of in-office IT security provisions are not built on the assumption that resources will even need to be taken offsite or accessed remotely, much less used from home.
Right off the bat, the single biggest thing we have seen missed in the remote working rush was to ensure that devices, systems and software sent out into remote working rotation were fully protected. By this we mean:
Ensuring that all devices, operating systems and software are:
- updated, with the latest patches applied
- set to have subsequent patches automatically applied
- updated to the latest supported OS and software versions available (both business and security software)
- accounted for on both corporate and BYOD devices
Updating and protecting passwords and credentials on all devices, operating systems and software, including:
- Changing default passwords on home Wi-Fi routers (notorious targets for brute force cyber-attacks)
- Ensuring employees are using different, strong passwords on each and every account and devices
- Enabling and configuring Multifactor Authentication wherever possible and available
These steps go a LONG way to wrapping some better protections around your remote workforce by reducing your attack surface.
However, to really shore up your protections AND make sure you can securely transition your devices and people BACK into the office, and out again, if needed, there are some other must-consider security items it’s high time to take a look at.
10 ways to build a secure remote working environment
Aside from number 1 , which we looked at above, there are 9 other actions we recommend businesses now circle back around to if they are committed to getting remote work security right!
Our Top 10 Remote Working IT Security Steps Checklist
- Ensure devices, systems & software are fully protected
- Encrypt Devices Wherever Possible
- Create a Secure Connection Back to the Office
- Scan and Secure Email and Build Phishing Awareness
- Enable Web Filtering
- Enable Use of Cloud Storage for Files and Data
- Manage Use of Removable Storage and Other Peripherals
- Control Mobile Devices
- Make Sure People Have A Way to Report Security Issues
- Make Sure You Know About “Shadow IT” Solutions
Why bother? Who knows what will come next?
Getting IT security right at a time of broader business uncertainty is something that will give your management team, your board, your stakeholders, your team and your customers some peace of mind and reassurance that you’re committed to the long haul and that you’ve taken prudent steps to prevent unnecessary risk or financial fall-out down the track over and above what people are already having to face.
Alongside this, the unfortunate reality of COVID-19 is that the bad guys are not cutting businesses any slack! In fact, scammers are more active on an even bigger and more ruthless scale than ever before, precisely at a time when they believe IT admins and businesses are distracted and taking security short cuts.
Finally, no one knows what will come next – if we do return to offices sooner rather than later, then our devices and data will need to be secure and safe enough to bring back into the office. If we are at home for longer, or need to ramp up to remote working again at scale, now is the right time to make sure we have our IT security bases covered.
To find out more about how your remote working environment measures up against the Top 10 Remote Working IT Security Steps, give us a call on 1300 629 786 or Contact us today!
Maxsum Consulting is offering a Circle Back to IT Security: Remote-Working IT Security Review for a very limited time only.
Take advantage of a fixed-fee review of your current remote working set-up benchmarked against our Top 10 Remote Working IT Security Steps, and receive actionable advice on cost-effective steps you can take now to ensure you team can stay secure and productive remotely, safely transition back to the office when the time comes, or do it all again if you have to! Contact Maxsum on 1300 629 786 or right here for more details!